Request: Vulnerability in hoek package
There is a vulnerability in the hoek package which is required by hawk that request depends on.
Request depends on hawk version ~6.0.2. Updating to hawk version 7.0.0 would fix the problem.
All 29 comments
I tried just bumping to hawk v7.0.7 earlier today but the test broke. I had to jump off to do something else but I only got as far as this faster way to run the test:
npx taper tests/test-hawk.js
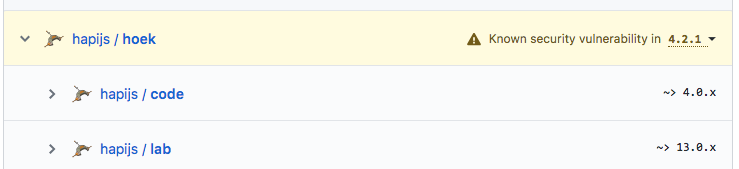
as far as i understand it, the issue is with a cve, https://nvd.nist.gov/vuln/detail/CVE-2018-3728, regarding hoek < v5.0.3; request v2.85.1 requires hawk ~6.0.2, which requires hoek 4.x.x. request requires hawk ~6.0.2 to maintain compatibility with node 4.
the cve states that “_hoek node module before 5.0.3 suffers from …_” and references https://github.com/hapijs/hoek/commit/32ed5c9413321fbc37da5ca81a7cbab693786dee as a fix in
hoek v5.0.3however,
hoek v4.2.1also has that fix:
https://github.com/hapijs/hoek/commit/5aed1a8c4a3d55722d1c799f2368857bf418d6df
https://github.com/hapijs/hoek/blob/v4.2.1/lib/index.js#L116
thus, it appears that the cve is incorrectly considering hoek v4.2.1 as vulnerable and may be why so many github repos are now reporting a vulnerability. i sent an email to nvd.nist.gov about the issue.
See here: https://github.com/request/request/issues/2891#issuecomment-372271727
To confirm the findings of dan-nl, both links from securityfocus and hackerone in the CVE state that it has been fixed
Not Vulnerable:
| Hoek Hoek 4.2.1
| Hoek Hoek 5.0.3
vdeturckheim posted a comment. Feb 15th (2 months ago)
Fix has been backported to 4.x track of the module and published as 4.2.1. (see https://github.com/hapijs/hoek/pull/231 )
and it's confirmed by @nlf in https://github.com/hapijs/hoek/issues/230#issuecomment-366056246
It has been fixed.
To further discuss, (…)
@warpdesign you said
Request depends on hawk version ~6.0.2. Updating to hawk version 7.0.0 would fix the problem
But how do I do that if I don't have hawk directly as a dependency?
[email protected] /home/jfolpf/autocosts
└─┬ [email protected]
└─┬ [email protected]
├─┬ [email protected]
│ └── [email protected] deduped
├─┬ [email protected]
│ └─┬ [email protected]
│ └── [email protected] deduped
├── [email protected]
└─┬ [email protected]
└── [email protected] deduped
which npm command? npm update request didn't do the job. Nor npm update hoek
thanks
You can't. You have to wait until Request publishes a new version that uses Hawk 7. That's the problem.
Can confirm, I've had 6 repos flagged by github for having the hoek vulnerability because of the request library.
@jfoclpf I guess it should be possible to temporary fix the problem by publishing forks with an updated version. But you don't want to go this road. Better wait for an official resolution (which shouldn't be long to come this the vce state just needs to be updated for hoek v4.2.1).
According to what I have been told from other packages, it's a false positive from github. There is no vulnerability in that version of hoek. Nonetheless it's annoying and thus let's wait for an official update of request.
The Node.js 4.x release line is going end of life April 30th, compatibility with it should not be a concern after then.
yes, hi :wave: hoek maintainer here. version 4.2.1 has been patched. github's alerts are currently wrong. i've submitted a request to correct the version range in the CVE and also harassed some kind folks at github to take care of things on their end. _hopefully_ they'll stop reporting that version as vulnerable soon.
https://github.com/request/request/issues/2926#issuecomment-385087487
version 4.2.1 has been patched
https://github.com/hapijs/hoek/issues/247#issuecomment-385012074
I submitted a request to update the CVE, hopefully that’ll happen soon and GitHub can get their db updated. Until that happens this is all out of my hands. I’m leaving this open in the hopes other people will find it.
!?
@dscalzi,
hawk > v7.0.0 drops support for node 4 and 6
https://github.com/hueniverse/hawk/blob/v7.0.1/.travis.yml
hawk >= v7.0.0 includes hoek 5.x.x
https://github.com/hueniverse/hawk/blob/master/package.json#L19
hoek v5.x.x drops support for node 4 and 6
https://github.com/hapijs/hoek/blob/v5.0.0/.travis.yml
How is this issue going now plz?
@diamont1001 it's already fixed
@Bjornskjald are u sure?
[email protected]/1 -> [email protected] -> [email protected]
@diamont1001 hoek 4.2.1 has the bugfix backported
@Bjornskjald
@diamont1001 because if you weren't lazy enough to read the whole discussion, you would see it's a bug with GitHub and hoek maintainer already contacted them...
@nlf Thanks for updating this thread earlier! Any response from Github yet? I'm considering pinging them as well...
status update?
status update?
@phillmv from @GitHub staff has posted an explanation at https://github.com/hapijs/hoek/issues/247#issuecomment-386708295:
[...] We fixed the versions we alert on back on Monday, and I personally deleted all the bad alerts earlier today. [...]
Hi, I have read all the discussion but I am still having the issue.
I have run npm audit and reported me about 11 vulnerability to hoek package.
I have update it to 7.0.7 but nothing changed. I have also updated the hawk package as suggested above but still nothing changed.
Can you help me please?
@NadGu plz check your package-lock.json file first.
@diamont1001 done right now. The version of hoek is 4.2.1. What can I do to update it?
[email protected] is ok.
I think that u just have to wait for github to refresh the data, at least I did it at the time, and it worked.
@diamont1001 So let's wait! At least I did all that I could. Thank you!
@nadgu Hi!
Are you saying you have a repository on GitHub where we're still flagging a version of 4.2.1 as being vulnerable? That shouldn't be happening!
Please email [email protected] with the repository link and mention @phillmv and we'll take it from there :).
This issue has been automatically marked as stale because it has not had recent activity. It will be closed if no further activity occurs. Thank you for your contributions.
Most helpful comment
yes, hi :wave: hoek maintainer here. version 4.2.1 has been patched. github's alerts are currently wrong. i've submitted a request to correct the version range in the CVE and also harassed some kind folks at github to take care of things on their end. _hopefully_ they'll stop reporting that version as vulnerable soon.